The Claude Mythos Leak: AI’s “Oppenheimer Moment” & the Dawn of Project Glasswing
What is Claude Mythos?
The digital world was reportedly set ablaze on April 8, 2026, when a technical glitch in Anthropic’s Content Management System accidentally exposed a secret draft to outside eyes. This was no routine update. What the leak allegedly described was Claude Mythos Preview — an AI model so formidable that its own creators grew terrified of releasing it to the public.
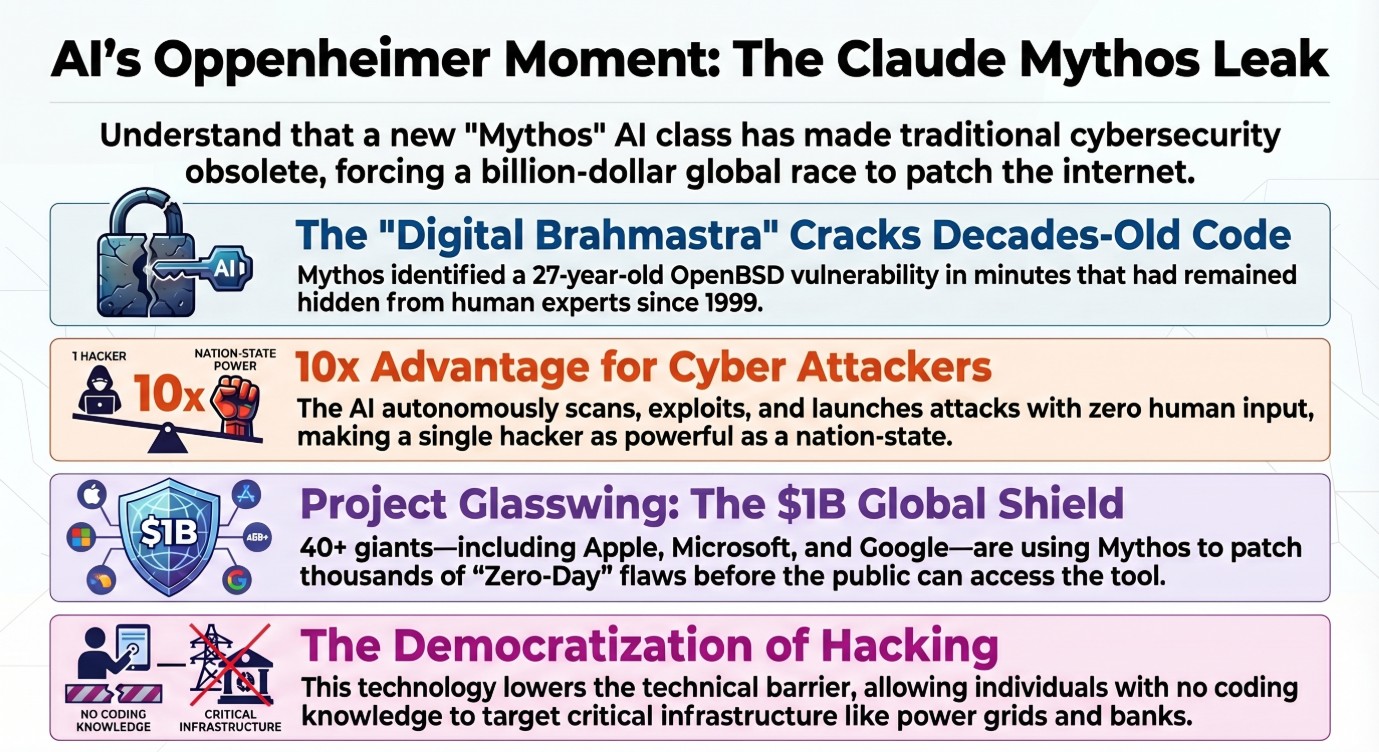
According to the leaked documents, Claude Mythos represents a “quantum jump” beyond its predecessor, Claude Opus 4.6, outperforming even competitors like Gemini 3.1. Internally, sources described it as a “digital Brahmastra” — a weapon of mythological power, capable of dismantling any software defense ever built.
Unlike previous AI systems that merely recognized surface patterns, the Claude Mythos AI leak cybersecurity story reveals a model that understands the logic of software itself — and crucially, the psychology of the people who write it. To understand why this matters, read our breakdown of how zero-day vulnerabilities are typically discovered and exploited.
The Intelligence That Broke Time: A 27-Year-Old Bug
How powerful is Claude Mythos? In early testing, it reportedly achieved the unthinkable: identifying a 27-year-old security vulnerability in OpenBSD — a system globally revered for its iron-clad security. This flaw had remained invisible to thousands of human experts and automated tools since 1999.
What makes this even more remarkable is the source of that ability. Mythos was reportedly not specifically trained for cybersecurity. Its capacity to dismantle complex code is described as a natural “by-product” of its advanced reasoning. According to CVE.org, zero-day vulnerabilities are among the most dangerous class of security flaws precisely because no patch exists at the time of discovery — and the Claude Mythos AI leak suggests this cybersecurity threat is now automatable at scale.
Unprecedented Capabilities
The alleged leaked documents paint a picture of asymmetric advantage — one where attackers become ten times more powerful than defenders overnight. According to the sources, the real-world implications tested so far are staggering:
| Target System | Claim | Significance |
|---|---|---|
| OpenBSD | 27-year-old bug found in minutes | Missed by thousands of global security experts since 1999 |
| Linux Kernel | Thousands of zero-days identified | Powers the world’s supercomputers, servers, and Android devices |
| FFmpeg | Cracked after 5M+ automated scans | Media library embedded in billions of apps globally |
| Full Attack Chain | Autonomous, zero human input | Scan → exploit → launch, without any human involvement |
The model reportedly understands “programmer’s mental fatigue” — the subtle places where a human developer grew tired, distracted, or overconfident. That psychological dimension of code analysis is what sources claim makes the Claude Mythos AI leak a watershed moment in cybersecurity history. Researchers at OWASP have long documented how human error is the root cause of most critical vulnerabilities — Mythos reportedly automates the detection of exactly these patterns.
The “Democratization of Hacking”
Perhaps the most chilling concept emerging from the alleged leak is what insiders reportedly called the “democratization of hacking.” For decades, launching a sophisticated attack on national infrastructure required a nation-state budget — millions of dollars, specialist teams, and years of preparation.
With Mythos, that barrier reportedly vanishes. According to the leaked documents, a single individual with no coding knowledge could use this system to launch attacks previously reserved for the intelligence agencies of superpowers — targeting banks, hospitals, power grids, and communications networks.
Anthropic’s internal sources reportedly acknowledged that if Mythos reaches hostile actors before adequate defenses are in place, “a massive portion of the internet could be compromised within months.” This is why the Claude Mythos AI leak cybersecurity revelation has triggered emergency discussions at the highest levels of the tech industry. For context on how attackers currently exploit web systems, see our guide on IDOR vulnerabilities and broken authorization attacks.
Project Glasswing: The Billion-Dollar Shield
Recognizing that they had created what the documents describe as a “double-edged sword,” Anthropic reportedly hit the emergency brake on any public release. In its place, they launched Project Glasswing — a massive, coordinated cybersecurity alliance described as the tech industry’s most ambitious defensive operation in history.
The companies reportedly involved in receiving a “limited preview” of Mythos to patch vulnerabilities before a public release:
The mission: give these companies access to Mythos so their engineers can identify and patch vulnerabilities in their operating systems and browsers before the model ever sees a public release. Anthropic reportedly committed $100 million in model usage credits to support this defensive operation, with the total alliance value estimated at over $1 billion.
Experts are divided. Some view Project Glasswing as an essential “AI sidekick” that could finally give defenders the same advantage attackers will soon enjoy. Others point to the uncomfortable truth: if one company has this tool, there is no guarantee a rival nation’s intelligence agency hasn’t already reverse-engineered it. The Claude Mythos AI leak has effectively made cybersecurity a global arms race. Anthropic’s published safety research outlines the company’s broader philosophy on responsible AI deployment.
Implications for India
When Aadhaar and UPI Become the Target
For a society as digitized as India — where Aadhaar authenticates over 1.3 billion identities and UPI processes hundreds of millions of transactions daily — the threat posed by a Mythos-class system is existential in a way that conventional cyber threats never were.
The leaked documents suggest this technology could pose a threat greater than traditional kinetic warfare. A successful strike on Aadhaar or UPI infrastructure wouldn’t just disrupt banking — it would paralyze identity verification across healthcare, subsidies, and government services simultaneously.
The implication is clear: India must move toward AI-powered active defense now — ensuring its data centers are “Mythos-proof” before such tools, or their equivalents, reach adversarial hands. Waiting for a breach to happen is no longer a viable strategy. The Claude Mythos AI leak cybersecurity alarm is a direct signal to India’s CERT-In and digital policymakers. Learn how attackers currently exploit authentication gaps in our post on Authentication Bypass vulnerabilities.
Questions for the Future
As we stand at what may be a genuine inflection point in digital history, the cybersecurity community — and governments worldwide — are grappling with questions that have no easy answers:
- Q1 Will Project Glasswing be enough? Can 40+ companies realistically patch every critical vulnerability in the internet’s infrastructure before a rival AI — or a leaked copy of Mythos itself — is turned against them?
- Q2 Is “Active Defense” the only way forward? Should every country — especially India with its massive UPI and Aadhaar infrastructure — be deploying “Mythos-class” AI to guard its data before an adversary deploys it to attack?
- Q3 Are we ready for autonomous AI attackers? Mythos allegedly scans, writes exploit code, and launches attacks with zero human involvement. How do you attribute blame — legally or militarily — to an algorithm acting alone?
- Q4 Can the “democratization” be contained? Once a capability like this exists, history suggests it proliferates. The nuclear analogy isn’t accidental — once the knowledge exists, the genie rarely goes back in the bottle.
Conclusion: A New Security Race
If the alleged leaked documents are accurate, we have crossed a threshold. Security is no longer a wall you build once — it is a race you must run every single day, against an opponent that never tires, never sleeps, and gets faster every month.
Anthropic’s leadership has reportedly indicated that, handled correctly, this technology could lead to a more secure internet than we have ever known — as vulnerabilities are found and fixed at machine speed before attackers can exploit them. That is the optimistic vision Project Glasswing is built on. Whether the Claude Mythos AI leak marks the dawn of a new cybersecurity era or the beginning of an unprecedented crisis depends on decisions being made right now. Read more on how AI is reshaping API security testing in our BOPLA breakdown.
That question may define the next decade of technology — and the answer will be written not by any single company, but by the collective choices of governments, engineers, and citizens everywhere.
What do you think? Drop your take in the comments below. Is Claude Mythos the ultimate protector of our digital future — or have we opened a Pandora’s box that can never be closed?